
Computer Forensics
3Computers Seized and Examined
3Verify Computer Clock Accuracy
3Process of copying the hard drives
3Process of creating evidence files
3Transition to Detective Lydell Wall
3Evidence Files presented at Trial
Kirk Stockham, Modesto Police Department, Computer Forensic Investigator, member of High-Tech Task Team. He described his function:
Taking a look at computers, deciding what's on them, and when it was opened, setting up the computer for examination, doing so correctly. And we have had some data losses, so try to prevent that. . . . Yes. I help seize the computers, set them up for processing, and then look for data that might be relevant in the case.
~~Trial Testimony~~
Lydell Wall, Detective with the Stanislaus County Sheriff's Department assigned to the Sacramento Valley High-Tech Crimes Task Force. Wall is a computer examiner for the Task Force. Wall worked with the evidence files that Stockham created when he cloned the 5 hard drives.
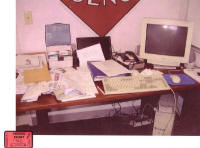
Seized on December 26, 2002, from 523 Covena, the Peterson residence, as shown in People's 174A-C
Dell Latitude laptop (174-B), named "Dell Laptop Home 1"
Compaq Armada laptop (174-C), named "Compaq Laptop Home 2"

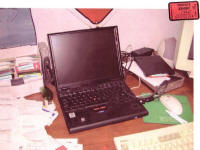
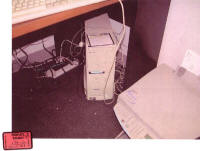
Seized on December 27, 2002, from the Warehouse Office on Emerald, as shown in People's 174D-H
IBM Thinkpad Laptop (174E-F), named "IBM Laptop Work 3"
Dell PC (174G-H), named "Dell Work PC 4"


Seized on February 18, 2003, by Officer Kip Loving, Turlock office of the High-Tech Task Force. Acquired by Stockham from Loving on February 24, 2003.
SOTEC notebook computer, named "SOTEC"
Verify computer clock accuracy
Stockham verified the accuracy of the clocks on the various computers by comparing them to the Atomic clock:
David Harris: And you compared these clocks on these computers to the atomic clock?
Kirk Stockham: Yes.
David Harris: And did you testify they were within two to three minutes of each other?
Kirk Stockham: Yes.
David Harris: So in your assessment, were the clocks in these computers pretty accurate?
Kirk Stockham: Yes.
Each file from a specific computer had the name given to that computer as part of its name. Example: Compaq Laptop Home was part of the file name for every file copied from that computer.
HARRIS: Now, looking at these two computers in 174-A, what was the naming standard, as you went through this process, starting with these two particular computers?
STOCKHAM: One with the "Spain" sticker on it that was labeled in an abbreviated form "Compaq Laptop Home". And the other one was labeled "Dell Laptop Home".
HARRIS: And if anybody were to look at these hard drives, would that particular file information be kind of burned into a hard drive so you can tell which computer it came from?
STOCKHAM: It wouldn't be burned into a hard drive. But the copied files that I create would have those file names, and so another examiner could work with my work and do it very easily, and know what he's working with because of these file names.<<<
STOCKHAM: Yes. The EnCase software allows you to file naming standards or labels, as I have testified previously. And once you do that, the EnCase copy files can be stored on my hard drives, and I can sift through the data and see what those computers have.
~~Trial Testimony~~
Process of copying the hard drives
Special forensic software used to catch the first byte of a hard drive, the last byte, and everything in between. The forensic copy is then analyzed for evidence, and the original hard drive is left intact for defense experts or for later recopying.
STOCKHAM: Yes. Most laptops allow you to do a fairly harmless disassembly of that part of the computer. The hard drive slips or slides in, depending how it's fastened to the circuitry. These were fairly easy. Once they were out of their cases, I had to take off the framing for the cartridge and expose the actual laptop and the pin connectors. Then I would hook that up to my computer forensic machines and make forensic copies of the laptop hard drives.
HARRIS: What's the forensic copy?
STOCKHAM: A forensic copy is a, like a bitstream copy where no data is lost. It's actually a very good clone of a hard drive. If done with forensic software, it catches the first byte of the hard drive, the last byte, and copies everything in between.
HARRIS: Let me they just back up. You are using a bunch of different terms. What is a bitstream?
STOCKHAM: Well, computer data is zeroes and ones on bits of data. You can copy a hard drive without affecting the original drive. You can actually do a copy that is so perfect of the original that you can do your examination on the copy and leave the original intact so there is no damage done. Because we never know if these hard drives are in good repair or not. So the first hurdle to protect the original drive is to copy it as a perfectly forensic copy. And once that's done, we can put the original hard drive aside for the defense experts later, or for recopying, and we can kind of do a free-for-all examination of the copied drives what malfunction or mistakes wouldn't affect the original hard drive. It's the first hurdle we like to get over.
Process of creating evidence files
Stockham and Wall primarily worked with the 2 home laptops and the work laptop and work PC. Wall said he used the Encase software to search these 4 hard drives (the forensic copy) simultaneously. Encase provides scripts to search by keyword or file type, and then sort by date.
Wall completed searches based on requests from the Modesto Police Department.
HARRIS: So as part of this process, I want to talk about that. Would they give you certain information to look for to see if you could find it on the computers?
WALL: Yes. They were interested in specific dates. And they were also interested in specific keywords to be looked at to see if they could be associated with any files that might have been created.
HARRIS: Were you asked to also go through and see if you could, if there were any e-mails on these computers?
WALL: Yes, I was.
HARRIS: And did you, were you asked to see if you could go through and find out if there had been any internet usage besides e-mails?
WALL: Yes.
HARRIS: Basic things of that nature, is that what they were asking you to do?
WALL: Yes. And specific dates.
~~Trial Testimony~~
Encase by Guidance Software
Wall testified that Stockham used Encase to create a set of image files which Wall then analyzed
SnapBack by Columbia Data Products
a forensic PC in Stockham's lab.
STOCKHAM: These are computers that have features that we like to make forensic software work properly. And they are computers that allow us to hook up other hard drives and other devices to them so we can get the lab work to get these copies done and the data reviewed. We actually use these machines where we put the forensic copies to actually look for data from these copied hard drives.
~~Trial Testimony~~
Transition to Detective Lydell Wall, a member of the High-Tech Task Force
Stockham's retirement on May 1, 2003 mandated that Wall take over the examination of the 5 computers.
Evidence Files presented at Trial
Defense Exhibit 5M (not admitted by stipulation)
People's Exhibit 177: Computer records - Temporary Internet Files